03. [30p] Kernel Samepage Merging
KSM is a page de-duplication strategy introduced in kernel version 2.6.32. In case you are wondering, it's not the same thing as the file page cache. KSM was originally developed in tandem with KVM in order to detect data pages with exactly the same content and make their page table entries point to the same physical address (marked Copy-On-Write.) The end goal was to allow more VMs to run on the same host. Since each page must be scanned for identical content, this solution had no chance of scaling well with the available quantity of RAM. So, the developers compromised to scan only with the private anonymous pages that were marked as likely candidates via madvise(addr, length, MADV_MERGEABLE).
[10p] Task A - Check kernel support & enable ksmd
First things first, you need to verify that KSM was enabled during your kernel's compilation. For this, you need to check the Linux build configuration file. Hopefully, you should see something like this:
# on Ubuntu you can usually find it in your /boot partition $ grep CONFIG_KSM /boot/config-$(uname -r) CONFIG_KSM=y # otherwise, you can find a gzip compressed copy in /proc $ zcat /proc/config.gz | grep CONFIG_KSM CONFIG_KSM=y
If you don't have KSM enabled, you could recompile the kernel with the CONFIG_KSM flag and try it, but you don't have to :)
Moving forward. Next thing on the list is to check that the ksmd daemon is functioning. Any configuration that we'll do will be through the sysfs files in /sys/kernel/mm/ksm. Consequently, you should change user to root (even sudo should not allow you to write to these files.)
- /…/run : this is 1 if the daemon is active; write 1 to it if it's not
- /…/pages_to_scan : this is how many pages will be scanned before going to sleep; you can increase this to 1000 if you want to see faster results
- /…/sleep_millisecs : this is how many ms the daemon sleeps in between scans; since you've modified pages_to_scan, you can leave this be
- /…/max_page_sharing : this is the maximum number of pages that can be de-duplicated; in cases like this it's better to go big or go home; so set it to something like 1000000, just to be sure
There are a few more files in the ksm/ directory. We will still use one or two later on. But for now, configuring the previous ones should be enough. Google the rest if you're interested.
[10p] Task B - Watch the magic happen
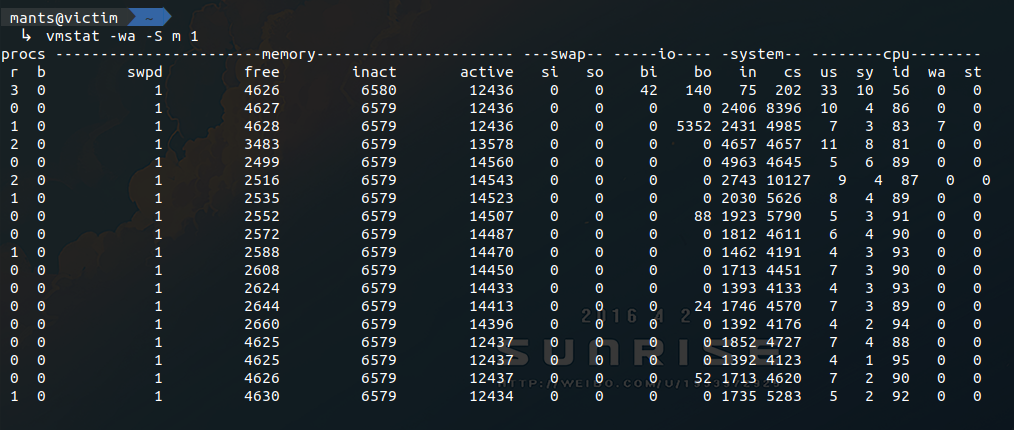
For this step it would be better to have a few terminals open. First, let's start a vmstat. Keep your eyes on the active memory column when we run the sample program.
$ vmstat -wa -S m 1
Next would be a good time to introduce two more files from the ksm/ sysfs directory:
- /…/pages_shared : this file reports how many physical pages are in use at the moment
- /…/pages_sharing : this file reports how many virtual page table entries point to the aforementioned physical pages
For this experiment we will also want to monitor the number of de-duplicated virtual pages, so have at it:
$ watch -n 0 cat /sys/kernel/mm/ksm/pages_sharing
Finally, look at the provided code, compile it, and launch the program. As an argument you will need to provide the number of pages that will be allocated and initialized with the same value. Note that not all pages will be de-duplicated instantly. So keep in mind your system's RAM limitations before deciding how much you can spare (1-2GB should be ok, right?)
The result should look something like Figure 1:
If you ever want to make use of this in your own experiments, remember to adjust the configurations of ksmd. Waking too often or scanning to many pages at once could end up doing more harm than good. See what works for your particular system.
Include a screenshot with the same output as the one in the spoiler above.
Edit the screenshot or note in writing at what point you started the application, where it reached max memory usage, the interval where KSM daemon was doing its job (in the 10s sleep interval) and where the process died.
[10p] Task C - Plot results
Now that you’ve observed the effects of KSM using vmstat, it’s time to visualize them. Solve the TODOs from plot.py from skeleton to generate a real-time plot that shows free memory, used memory, and memory used as a buffer over time, based on the freemem column from the output of the vmstat command.
If you get something resembling Could not load the Qt platform plugin “xcb” in ”” even though it was found. on either WSL or certain Linux environments (e.g., having Hyprland as a Wayland compositor), check out
this post.